Imagine trying to vote in an election where anyone can create a thousand fake identities and cast a thousand votes. That’s a Sybil attack-and it’s one of the biggest threats to any decentralized system. Without a way to stop it, a single person could control a network, manipulate transactions, or drain wallets. But blockchain networks like Bitcoin have a built-in defense: Proof of Work. It’s not magic. It’s math, electricity, and hardware working together to make cheating too expensive to even try.
What Is a Sybil Attack?
A Sybil attack happens when one attacker creates many fake identities-called Sybil nodes-to gain control over a network. In a social network, this could mean spamming users with fake profiles. In a blockchain, it means flooding the network with fake nodes that pretend to validate transactions. If left unchecked, these fake nodes could lie about which transactions are valid, reverse payments, or block new ones. The goal? To break trust in the system.
Early digital systems tried to solve this with identity verification-like requiring email or phone numbers. But blockchains are designed to be permissionless. No ID checks. No government records. No central authority. So how do you stop someone from making 10,000 fake identities with zero cost? The answer came with Bitcoin’s 2008 whitepaper: make participation expensive.
How Proof of Work Works
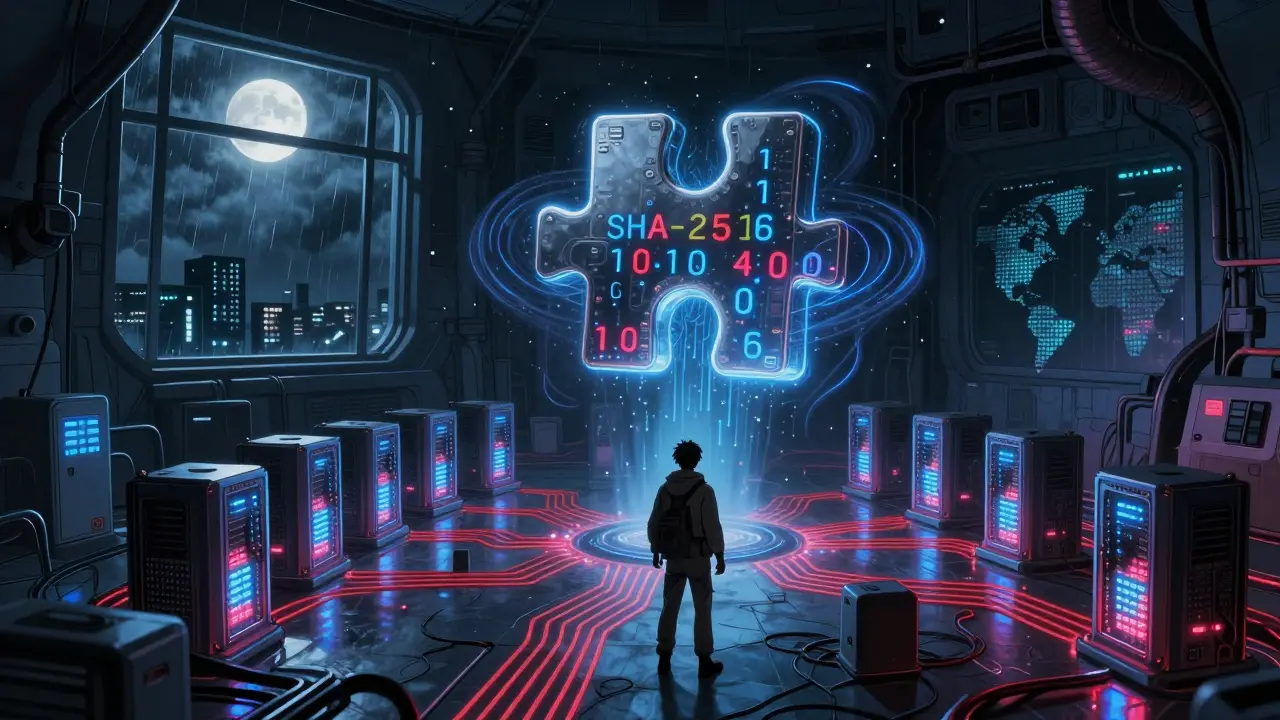
Proof of Work (PoW) forces miners to solve a hard math puzzle before they can add a new block to the blockchain. This puzzle isn’t just hard-it’s designed to take real time and real energy to solve. Bitcoin uses the SHA-256 algorithm, which as of 2025 requires roughly 2^67 operations to find a valid solution for each block. That’s over 147 quintillion tries on average.
Miners don’t guess randomly. They use specialized hardware called ASICs-tiny computers built for one thing: solving these puzzles faster than anyone else. Each ASIC miner, like the Bitmain Antminer S21 released in October 2025, costs $4,200 and uses 3,350 watts of power. It can do 200 terahashes per second. That’s 200 trillion guesses every second.
Here’s the key: every time you want to participate in validating transactions, you have to spend real money. Not tokens. Not digital credentials. Real cash on hardware, electricity, cooling, and maintenance. If you try to flood the network with fake nodes, you’d need to buy thousands of these machines, power them, and keep them running. The cost isn’t just high-it’s physically impossible for most attackers to afford.
Why Proof of Work Stops Sybil Attacks
Proof of Work turns identity into a commodity. You can’t fake it. You can’t copy it. You can’t clone it. To become a valid node, you need to prove you’ve spent resources. That’s the core idea behind its Sybil resistance.
Think of it like a voting system where each vote costs $10,000. Even if someone had $1 billion, they could only buy 100,000 votes. But the network has over 15,000 active nodes spread across 96 countries, according to Bitnodes.io data from December 2025. To control the majority, an attacker would need to own more than half of the total computing power-the infamous 51% attack.
As of December 2025, Bitcoin’s total hash rate is 650 exahashes per second (EH/s). To control 51%, you’d need about 332 EH/s. According to the Cambridge Centre for Alternative Finance, that would cost over $12.7 billion in hardware alone, plus $1.8 million every day just in electricity. Bitcoin’s market cap? Around $1.2 trillion. So even if you spent $14.5 billion to launch the attack, you’d only be able to steal a fraction of that value-and everyone would know it was you. The price of the attack would crash the very asset you’re trying to steal.
That’s why Bitcoin has never had a successful 51% attack in its 16-year history. The cost is too high. The risk is too great. The reward is too small.
PoW vs. Other Systems
Proof of Stake (PoS), used by Ethereum since 2022, asks validators to lock up cryptocurrency as collateral. On Ethereum, you need 32 ETH-worth about $100,000 as of late 2025-to become a validator. That’s expensive, but it’s still digital. You can borrow ETH. You can rent it. You can simulate it. PoW doesn’t allow that. You can’t borrow electricity. You can’t rent an ASIC. You can’t fake a power bill.
Smaller blockchains using PoW have been attacked. Ethereum Classic suffered three 51% attacks in 2020, costing over $5.6 million in double-spent transactions. Why? Because its hash rate was low-under 1 EH/s. Attackers could rent enough mining power for a few hours and slip through. But Bitcoin? It’s too big. Too expensive. Too slow to move.
That’s why PoW isn’t used everywhere. It’s too heavy for IoT devices, mobile apps, or low-power networks. But for high-value systems where security matters more than speed? It’s unmatched.
Real-World Impact
Bitcoin processes $18.3 billion in transactions every day, according to Glassnode. JPMorgan’s Onyx division uses Bitcoin for $1.2 billion in daily institutional settlements. These aren’t speculative trades. These are real financial flows. And they rely on PoW’s ability to say: “No one can fake their way in.”
On Reddit, users who run full Bitcoin nodes say they feel safer because of it. One user, u/BlockchainGuardian, wrote: “I’ve run a full node since 2017, and the fact that attackers would need billions in hardware to override my validation gives me confidence.” That’s not hype. That’s math.
But it’s not perfect. Critics point out that mining is becoming centralized. Most ASICs are made by two companies: Bitmain and MicroBT. Most mining happens in places with cheap electricity-like Texas, Kazakhstan, or Georgia. That creates a risk: if a single country shuts off power or seizes hardware, it could disrupt the network. Dr. Aggelos Kiayias from the University of Edinburgh warns this could undermine Sybil resistance over time.
Still, the numbers don’t lie. The MIT Digital Currency Initiative’s 2025 report found that PoW networks with over $10 billion in market cap have shown “exceptional resilience” against Sybil attacks. Bitcoin, with its $1.2 trillion value, is the gold standard.

Future Challenges
One looming threat? Quantum computing. IBM announced a 1,121-qubit processor in December 2025. If quantum computers become powerful enough, they could break SHA-256. But that’s still years away-possibly decades. The Bitcoin community is already researching quantum-resistant cryptography. The network can upgrade. It has before.
Another development? Layer 2 solutions. Blockstream’s Liquid Network, upgraded in December 2025, now includes “proof of physical resources” verification for institutional transactions. It’s not replacing PoW-it’s reinforcing it. For high-value transfers, you still need real hardware. You still need real cost.
Meanwhile, regulators are watching. The EU’s MiCA rules, effective January 1, 2026, now require PoW blockchains to disclose their carbon footprint. That doesn’t kill PoW-it forces transparency. And for now, the market still values security over efficiency.
Bottom Line
Proof of Work isn’t elegant. It’s not fast. It’s not green. But for stopping Sybil attacks, it’s the most reliable system we’ve ever built. It turns trust into something you can measure: kilowatts, terahashes, dollars spent. You can’t lie your way into Bitcoin. You have to earn it-with electricity, with hardware, with time.
That’s why, despite all the alternatives, Bitcoin’s PoW still stands tall. Not because it’s perfect. But because it’s the only system that makes cheating so expensive, it’s not worth the risk.




Mohammed Tahseen Shaikh
March 24, 2026 AT 00:05manoj kumar
March 25, 2026 AT 23:27Mike Yobra
March 26, 2026 AT 19:26Anand Makawana
March 28, 2026 AT 00:05John Alde
March 29, 2026 AT 12:58Anna Lee
March 29, 2026 AT 17:39Tammy Stevens
March 31, 2026 AT 12:25Andrew Midwood
April 1, 2026 AT 17:44Brad Zenner
April 2, 2026 AT 04:04Neil MacLeod
April 2, 2026 AT 07:29Alice Clancy
April 3, 2026 AT 22:24Marie Mapilar
April 4, 2026 AT 01:46Justin Credible
April 5, 2026 AT 00:00Pradip Solanki
April 5, 2026 AT 16:14