Think of a blockchain as a digital book where every page is locked with a unique seal. If someone tries to change a single word on page five, the seal breaks, and every subsequent page in the book suddenly looks wrong. This isn't magic; it's the basic blockchain block structure that keeps your digital assets and data safe. But what actually goes inside one of these "pages"?
The Big Picture: What is a Block?
At its simplest, a block is just a container for data. In the world of crypto, that data is usually a list of transactions-who sent how much to whom. However, a block is more than just a list; it's a tightly packed bundle of information that includes a header (the "label") and a body (the "content").
Each block functions as a permanent record. Once it's filled and verified, it's closed and linked to the one before it. This creates a chronological chain that anyone can verify but nobody can silently edit. If you've ever wondered why people call it "immutable," it's because of how these components lock together.
Breaking Down the Block Header
The header is the most critical part of the block for security. It doesn't contain the transactions themselves, but rather the metadata that proves the block is valid. Imagine it as the envelope of a letter; it tells you where it's from, when it was sent, and contains a security seal.
Block Header is the metadata section of a block that contains the cryptographic pointers and timestamps necessary to link blocks together. It typically consists of several key fields:
- Version: This tells the network which set of software rules this block follows. As blockchain protocols upgrade, the version number helps nodes stay in sync.
- Timestamp: This is the exact second the block was created. It prevents "replay attacks" and ensures the sequence of events is undisputed.
- Previous Block Hash: This is the "glue." It is the digital fingerprint of the block that came immediately before this one.
- Merkle Root: A single hash that represents every single transaction inside the block body.
- Nonce: Short for "number used once." This is a random value that miners change repeatedly to solve the mathematical puzzle required to add the block to the chain.
The Secret Sauce: Cryptographic Hashing
You can't understand a block without understanding the hash. A hash is like a digital fingerprint. In systems like Bitcoin, the SHA-256 is a cryptographic hash function that turns any input data into a fixed 256-bit alphanumeric string .
Here is the wild part: if you change one tiny comma in a transaction, the entire hash changes completely. This is called the avalanche effect. Because the next block in the chain includes the hash of the previous one, changing a past block creates a domino effect. The current block's "previous hash" pointer will no longer match, and the network will instantly reject the tampered data as a fraud.
| Component | Role | What happens if it's changed? |
|---|---|---|
| Previous Hash | Links blocks together | The chain breaks immediately |
| Merkle Root | Summarizes transactions | Invalidates the block header |
| Nonce | Solving the mining puzzle | Block isn't accepted by the network |
| Timestamp | Chronological ordering | Possible network synchronization error |
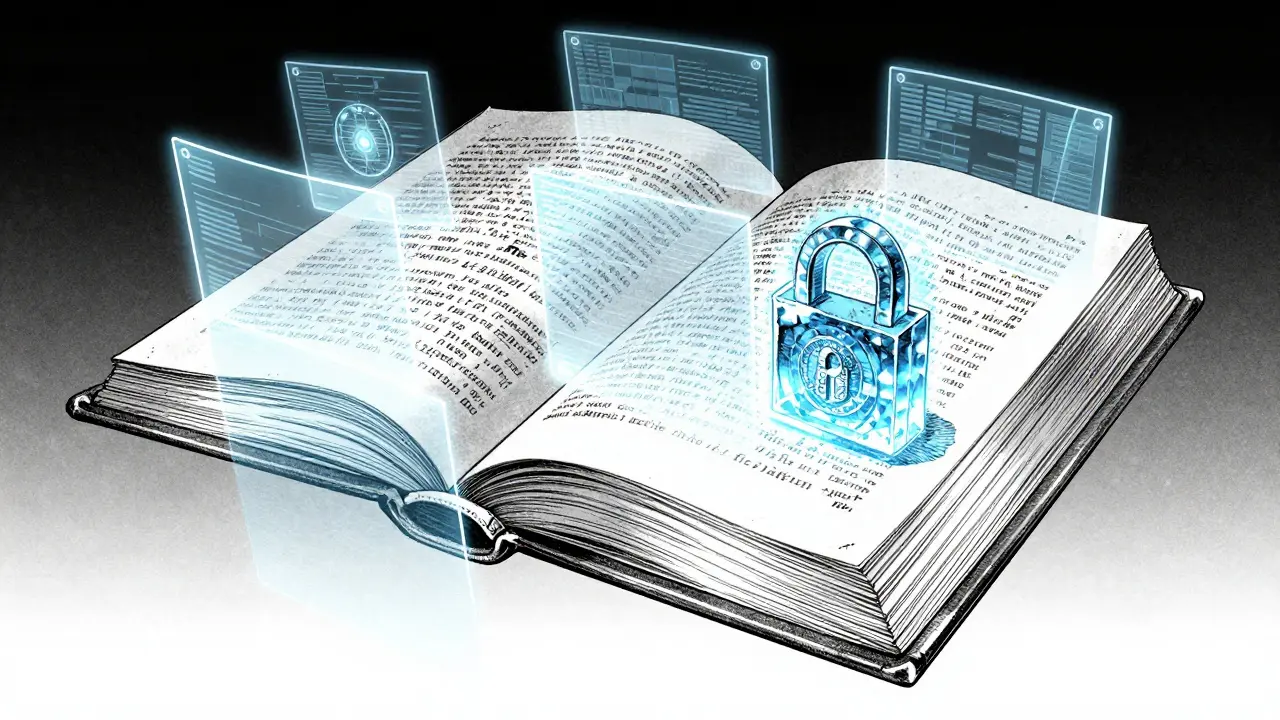
The Block Body and the Merkle Tree
While the header handles the security, the block body is where the actual work happens. This is the list of transactions. In a typical Bitcoin block, this includes the sender's wallet address, the receiver's address, and the amount of BTC transferred.
But listing thousands of transactions would make the header massive and slow. To solve this, blockchains use a Merkle Tree is a data structure that hashes pairs of transactions repeatedly until only one single hash remains . This final hash is the Merkle Root.
Why does this matter? It allows for "Simplified Payment Verification." Instead of downloading the entire block (which could be megabytes), a light wallet only needs the Merkle Root and a small piece of the tree to prove a transaction exists. It's like checking the index of a book instead of reading every single page to find one sentence.
How Blocks Reach Consensus
A block doesn't just appear. It has to be approved. This is where nodes-computers running the blockchain software-come into play. These nodes act as the jury. They check if the transactions are valid (e.g., does the sender actually have the money?) and if the hash of the block meets the required difficulty target.
In a Proof of Work system, miners compete to find the correct nonce. Once a miner finds a value that produces a hash starting with a specific number of zeros, they broadcast the block to the network. Other nodes quickly verify the work. If the majority agrees the block is legitimate, it's appended to the chain, and the miner gets a reward.
This decentralized verification means no single bank or government controls the ledger. The trust is shifted from a central authority to the math itself. If a hacker wanted to change a transaction in Block 100, they would have to re-mine Block 100, 101, 102, and every block created since then, faster than the rest of the entire global network combined. That's why the system is considered practically impossible to hack once a block has a few "confirmations" (blocks piled on top of it).
The Lifecycle of a Block: From Memory to Chain
- The Mempool: When you send crypto, your transaction goes into a waiting room called the memory pool (mempool).
- Block Assembly: A miner picks a group of transactions from the mempool, calculates the Merkle Root, and fills in the header.
- The Hashing Race: The miner guesses millions of nonces per second, hoping to find a hash that meets the network's difficulty requirement.
- Propagation: Once a solution is found, the block is sent to all other nodes.
- Validation: Nodes check the transactions and the hash. If everything matches, they add the block to their local copy of the ledger.
- Finalization: As new blocks are added on top, the old blocks become deeper in the chain and more secure.
What happens if two miners find a block at the same time?
This creates a temporary "fork" in the blockchain. The network will temporarily have two different versions of the latest block. However, the protocol resolves this through the "longest chain rule." Miners will start building on whichever version they saw first. Eventually, one chain becomes longer than the other. The shorter chain is discarded (these are called "orphan blocks"), and the entire network converges on the longest valid chain.
Can the data inside a block ever be deleted?
In a standard public blockchain, no. Because each block's hash depends on the previous one, deleting a block would break the link for every single block that follows it. To delete data, you would essentially have to rewrite the entire history of the blockchain from that point forward, which would require controlling over 51% of the network's computing power.
Is the nonce a part of the transaction data?
No, the nonce is strictly part of the block header. It doesn't affect the transactions themselves; it is only used by miners to change the overall hash of the block header until it satisfies the network's difficulty target.
How does the Merkle Root prevent fraud?
The Merkle Root is a cryptographic summary. If a single bit of data in any transaction in the block is changed, the resulting hash of that transaction changes. This change bubbles up the tree, completely altering the Merkle Root in the header. Since the header's hash is what the rest of the network verifies, any fraud in the block body is immediately visible in the header.
Does every blockchain use the same block structure?
While the core concepts (header, body, and hashing) are similar, different blockchains have different specifications. For example, Ethereum uses "Accounts" and "State Roots" to track balances, whereas Bitcoin uses a "UTXO" (Unspent Transaction Output) model. Some blockchains also have different block times-Bitcoin blocks are found roughly every 10 minutes, while others might be found every few seconds.




Lauren Abrams
April 13, 2026 AT 07:50The part about the Merkle Root is actually pretty cool. It makes a lot of sense why you wouldn't want to download the whole thing just to check a transaction.
Scott Fenton
April 15, 2026 AT 05:34It is important to note that while Proof of Work is the most well-known consensus mechanism, many modern blockchains have transitioned to Proof of Stake to reduce energy consumption. This change alters the role of the nonce and the mining race entirely, as validators are chosen based on the number of coins they hold rather than computational power. This shift addresses the scalability and environmental concerns associated with SHA-256 hashing at a global scale.
Terrance Hausmann
April 15, 2026 AT 21:59Everyone is just learning and that is the beauty of this tech. Just keep diving deeper into how the nodes actually communicate because that is where the real magic happens, and don't let the complexity scare you off since we all started from zero.
Tracie and Matthew Hartley
April 16, 2026 AT 17:45plz tell me why i shud care about a digitall book when banks already do this stuff lol. sounds like a lot of hype for sum math
Will Dixon
April 17, 2026 AT 21:09it basically means no one person can just change the numbers like a boss would at a job
Carroll Foster
April 19, 2026 AT 09:39Oh sure, because nothing says "decentralized utopia" like a massive energy sinkhole running SHA-256 cycles just to prove some arbitrary nonce. The throughput is basically a joke compared to centralized databases, but hey, at least we have the privilege of waiting ten minutes for a confirmation while the network congestion hits an all-time high. Absolute peak efficiency right here.
Omotola Balogun
April 19, 2026 AT 23:13The author missed a crucial point about the difficulty adjustment. The network doesn't just have a target; that target shifts every 2016 blocks in Bitcoin to ensure blocks are found every ten minutes regardless of how much hash power enters the fray. Without this, the whole system would collapse as more miners joined the race. It is fundamental to the stability of the monetary policy embedded in the code.
Lane Montgomery
April 21, 2026 AT 05:20Too long. Just use a wallet.
Stanly Hayes
April 21, 2026 AT 07:03This stuff is basic. We need to push these standards globally if we actually want to move away from the old systems. Get with the program or get left behind!
Kelly Cantrell
April 21, 2026 AT 14:39It's funny how they talk about "trusting the math" but they don't tell you who actually writes the code for the nodes. If a few big companies control the software updates, the "decentralization" is just a front to make us feel safe while they track every single transaction on a public ledger. It's just another way for the system to keep tabs on us under the guise of innovation.
EDOZIEM MICHAEL
April 22, 2026 AT 13:31math is just the language of the universe and this is just a new way to write the truth
Chidinma Sandra okafor
April 23, 2026 AT 14:30Oh wow, a great explanation of a system that's probably going to crash and burn anyway. I love how we pretend this is the future while our own local infrastructure can't even keep the lights on. Truly a masterpiece of theoretical engineering that ignores reality entirely.
Alan Seiden
April 24, 2026 AT 09:58Absolute rubbish. The energy waste alone makes this a failure of human intelligence. Only an idiot would think that burning megawatts of electricity to solve a useless puzzle is a sustainable way to run a financial system. It is a scam wrapped in technical jargon to fool the gullible.
Akshay Gorad
April 24, 2026 AT 10:54I find the explanation of the block header quite clear. It helps in understanding why the security is so tight.
Mikayla Murphy
April 26, 2026 AT 05:23It's really interesting to see how different cultures are adopting this tech for different reasons. In some places, it's about freedom, in others, it's just a gamble. But the underlying math remains the same regardless of where you are in the world.
logan bates
April 27, 2026 AT 20:12America should be the one leading this tech and only this tech. We have the best compute power anyway.